Bots are more common today than at any point in the history of the internet. With the rise of AI and easy‑to‑use automation frameworks, spinning up a bot is no longer a task reserved for advanced attackers. Anyone with a few lines of Python or access to a proxy network can generate traffic that cascades across an infrastructure in seconds.
Bots themselves are not inherently bad. They power automation, monitoring, indexing, and countless legitimate workflows. But in the context of cybersecurity, the term “bot” takes on a very specific meaning: a component or utility that generates automated traffic with malicious intent.
This malicious traffic can spread across networks, exploit APIs, brute‑force identities, or even serve as the first stage of a malware or ransomware campaign. The natural question becomes: Can malicious bot traffic be prevented or detected?
The answer is both yes and no. There is no single control that stops all bots. Effective defense requires defense‑in‑depth, and more importantly, a Zero Trust mindset.
To understand why, we need to look at the two broad categories of bot traffic: HTTPS bots and non‑HTTPS bots.
1. HTTPS Bots: The Illusion of “Normal” Traffic
HTTPS bots are the most common type of malicious automation. They blend into normal web and API traffic, making them extremely difficult to detect using traditional security controls.
Credential Stuffing Bot — A Simple but Powerful Example
A threat actor can create a credential‑stuffing bot with just a few lines of Python:
POST /login
Content-Type: application/json
User-Agent: Mozilla/5.0{“username”: “john@example.com”, “password”: “Password123”}
This traffic looks completely legitimate:
- It uses real browser fingerprints
- It is sent over valid HTTPS
- It can be throttled to low-and-slow patterns to avoid rate limits
- It uses residential proxies to appear like normal home users
The bot simply cycles through leaked username/password pairs until it finds a match.
Why WAF Alone Is Not Enough
WAFs are excellent at blocking: Known CVE signatures, Malicious payloads, High‑rate brute force, Bad user agents…
But in this case:
- The request is clean
- The payload is valid JSON
- The User-Agent is legitimate
- The rate is controlled
- The IP looks normal
So the WAF sees nothing wrong. This is why WAF effectiveness against bots is partial at best.
API Security: The Next Line of Defense
API security tools shine where WAFs fall short. They can detect:
- Enumeration behavior
- Abnormal login patterns
- Role misuse
- BOLA attempts
- Repeated failures across many accounts
However, even API security eventually passes traffic to the backend. And that’s where the strongest control lives.
Application Logic: The Most Important Layer
The application itself holds the business logic. It knows what is normal and what is not. It can enforce:
- Device‑bound tokens
- MFA for abnormal behavior
- Account lockouts
- Impossible travel detection
- Workflow sequencing
- Identity‑based rate limits
This is where bots fail — not because of signatures, but because they cannot mimic business logic.
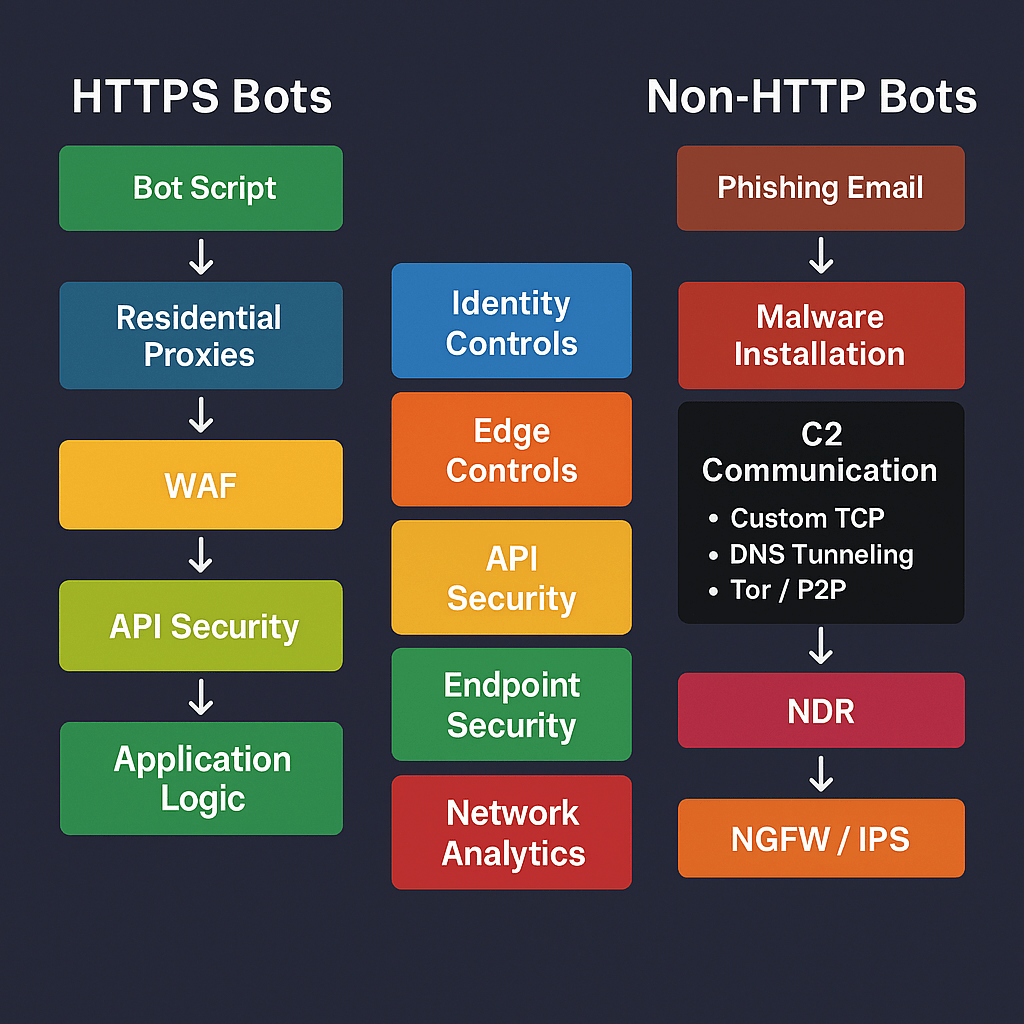
2. Non‑HTTPS Bots: The Invisible Threat
Not all bots use HTTP or HTTPS. Some of the most dangerous ones never touch your WAF or API gateway.
Malware Botnet C2 Bot — A Realistic Example
Consider a bot similar to Emotet or TrickBot.
How It Enters the Environment
- A user opens a phishing attachment
- Malware installs silently
- A background process launches
- The bot begins communicating with its command‑and‑control (C2) server
This communication often uses:
- Custom encrypted TCP
- DNS tunneling
- Tor
- Peer‑to‑peer protocols
None of this traffic is HTTP or HTTPS.
Why WAF and API Security Are Useless Here
These bots:
- Never hit your web apps
- Never touch your API gateway
- Never generate HTTP traffic
They operate entirely at the endpoint and network layers.
The Controls That Actually Work
EDR/XDR is the strongest defense:
- Detects malicious process behavior
- Blocks persistence mechanisms
- Stops lateral movement
- Flags suspicious PowerShell/Python scripts
- Kills the bot before it reaches its C2 server
NDR (Network Detection & Response) adds another layer:
- Detects DNS tunneling
- Flags unusual outbound TCP ports
- Identifies beaconing patterns
IPS/NGFW contributes by:
- Blocking known C2 IPs/domains
- Blocking Tor traffic
- Blocking unusual outbound ports
This is where Zero Trust becomes essential — every device, every process, every outbound connection must be continuously verified.
The Zero Trust Reality: No Single Tool Stops All Bots
Malicious traffic cannot be handled by one product or one layer. Bots exploit gaps — and gaps appear when organizations rely on a single control.
A Zero Trust approach requires:
- Strong identity controls
- Edge protections (WAF, bot management)
- API behavior analysis
- Application‑level business logic
- Endpoint protection (EDR/XDR)
- Network analytics (NDR, DNS security)
- Governance, discipline, and process maturity
Bots are evolving. Automation is cheap. AI makes it easier than ever to mimic human behavior. But with layered controls, strong application logic, and Zero Trust discipline, organizations can detect, contain, and stop both HTTPS and non‑HTTPS bots before they escalate into malware, lateral movement, or ransomware.




Leave a comment